SHA1:
- d7e3f5d3d223d3697b113540f7b3ad6b9df434e4
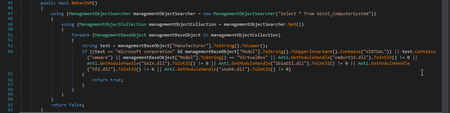
Downloader Trojan for Trojan.BtcMine.2894. Its self-designation is “Romeo”. The downloader is written in С#. Once launched, it runs a scan for virtual machines:
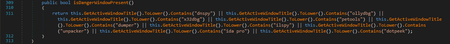
The Trojan also checks for a debugger in the system using the IsDebuggerPresent() function, and determines the number of opened windows using the following algorithm:
To make the analysis difficult, the malware damages the file’s Cor-header and modifies the import from kernel32.dll to NtContinue. When detecting a debugger, a virtual machine or “suspicious” windows, it shuts down.
The Trojan installs itself into the “%PROGRAMDATA%\<hwid>\<hwid2>.exe”, folder, where hwid is a string obtained from the registry key [HKLM\\SOFTWARE\\Microsoft\\Cryptography] 'MachineGuid', and hwid2 is the first five symbols of MD5 from hwid. The folder and the file are appended with the attributes “hidden” and “system”.
To bypass Windows User Accounts Control (UAC), the Trojan executes the following actions:
- sets the key [HKCU\\Software\\Classes\\mscfile\\shell\\open\\command] 'Userinit' = “C:\\Windows\\System32\\userinit.exe, <path>”, where <path> is a path to the Trojan installation folder;
- sets the key [HKCU\\Software\\Classes\\mscfile\\shell\\open\\command] '(default)' = “<path>”, where <path> is a path to the Trojan installation folder.
Following this, it creates a shortcut called “BootSys.url”, which points to the file “C:\\Windows\\System32\\eventvwr.exe”
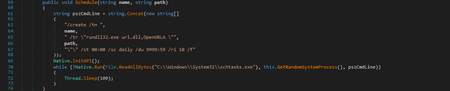
For its auto run, the Trojan uses the Windows Task Scheduler:
Following that, the Trojan starts installing Trojan.BtcMine.2894. It sends a request to the iplogger service (the service address is stored in the program’s body), and downloads the executable files of Trojan.BtcMine.2894 using the addresses stored in its own body. It then embeds these files into random processes running from the %SYSTEM32% folder.